By Blerim Abedini, ISSD-NM
In the year 2020– In a time of the pandemic, remote work was necessary, which simultaneously increased the activity of cyber attacks either as a reason for the financial or political crisis. Although states, businesses, and other organizations are aware of the great damage caused by cyber attacks, the negligence is still small.
A total of 304 million ransomware attacks worldwide in 2020. This was a 62 percent increase from the previous year. The Australian Cyber Security Centre (ACSC) shows that cyber security includes phishing emails and malicious software affecting larger organizations, supply chains, and government entities. In this case, the Toll Group suffered a cyber attack and it shut down all systems. The Australian Competition and Consumer Commission (ACCC) identified that Australians lost over $634 million from scammers. Globally, the CrowdStrike survey shows that 56% of respondents reported that their organization suffered a ransomware attack in 2020, with 27% of those who experienced a successful attack ending up paying ransom at an average cost of US$1.1 million. Another case with Marriot hotels is where the information of 5.2 million guests has been breached by attackers by using staff accounts as linking. Accounts of personalities on Twitter(cryptocurrency scam) including Barack Obama, Jeff Bezos, Elon Musk, Joe Biden, Mike Bloomberg, Bill Gates, Kanye West, Kim Kardashian, etc, are attacked by three individuals which earned them over $114,000 or approximately 13 bitcoins. These scammers are, British citizen Joseph O’Connor who was arrested for extradition to the US and he is charged with the illegal compromise of 130 Twitter accounts on July 15, 2020. Also, this attack includes the mastermind, a 17-year-old from Florida, Graham Ivan Clark who is sentenced to three years in prison.
Software AG is the second-largest company in Germany. It has more than 10,000 active customers, and 5,000 employees in 70 countries. A majority (70%) of Fortune 1000 companies in the world including Airbus, Telefonica, Lufthansa, DHL, Fujitsu, Credit Suisse, and Continental use Software AG’s products such as database systems, enterprise service bus (ESB) frameworks, and software architecture (SOA).
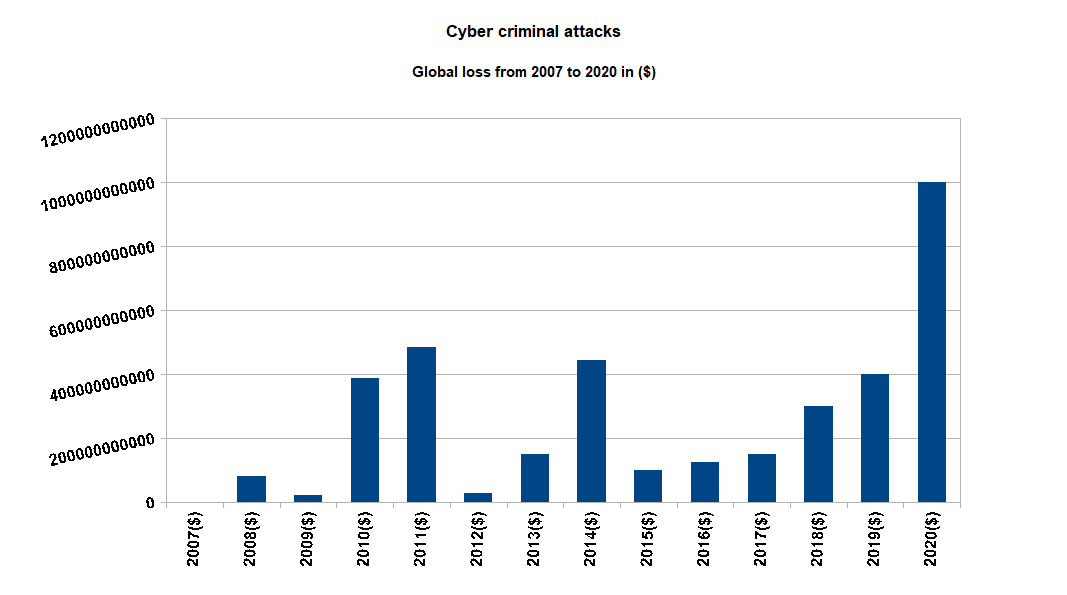
The German software giant was the victim of a double attack when a $20 million ransom was demanded, which Software AG declined to pay. As a result, the ransomware attackers published confidential data of employees such as passport details, internal emails, and financial information. A cybercriminal gang known as “Clop” confirmed that it was responsible for deploying the ransomware on Software AG’ IT infrastructure. The police in the year 2021 seized equipment from the alleged Clop ransomware. This includes computer equipment, several cars including a Tesla and Mercedes, and 5 million Ukrainian Hryvnia (around $185,000) in cash. See the video on youtube: https://youtu.be/PqGaZgepNTE?t=243 . These attacks first began in February 2019, when the group attacked four Korean companies and encrypted 810 internal services and personal computers. Since, Clop — often styled as “Cl0p” — has been linked to a number of high-profile ransomware attacks. These include the breach of U.S. pharmaceutical giant ExecuPharm in April 2020 and the attack on South Korean e-commerce giant E-Land that forced the retailer to close almost half of its stores. Around 1% of global GDP in 2020 is lost to cybercrime or 1 trillion dollars.
It is observed that even non-teenagers engage in cyber attacks as an easy way to earn money or get rich. Also, the category of attackers who confiscate data such as passports, and government data in this case demand a ransom compared to those who attack businesses, consumers, and workers. Economically stagnant states have not engaged cyber insurance agencies at an appropriate level. But, in some cases, even security agencies cannot protect institutions and businesses from hackers who find weak points to penetrate confidential data.
Sources:
www.logsign.com, www.techtarget.com, www.techradar.com, www.nortonrosefulbright.com, cybersecurityasean.com,techcrunch.com

